Almost A Dot Com Mogul
Filed Under Geek | 2006-10-10, 22:40
I stumbled onto John Chow’s blog tonight and found a post titled “Requirements To Be A Dot Com Mogul”. Let’s see….
* Your income is made from the Internet
Some of it is. At least my part-time re-invest and “toys” money is
* The minimum Internet income level is $10,000 a month (you can not add income from other sources to hit this $10K level)
Working on it. :)
* You have no jobs outside of the Internet
Not yet. I like the benefits of having a job still.
* You have a personal blog with your name as the domain name
Check
* Your blog must be updated at least once per week
Check. Although that should say blogs. I try to post new material at least once a week if not more.
* A Google search of your name must be at the #1 spot
how about #1 and 60% of the front page is related to me? (out of 140,000 results). Now if I could just figure out how to bump that football player who shares my name off the front page.
* You must be willing to help dot com mogul wannabes
Always there to lend a hand, an ear, a bit of advice, some code, a link, whatever.
So I’m part of the way there. Hopefully by this time next year I’ll be able to add the title “Dot Com Mogul” to my resume. Hey, that and a dollar will get me a cup of coffee.
Demographic Info From 26,000 Phished MySpace Account
Filed Under Geek | 2006-10-10, 19:10
So a few days ago LoLo tapped me for some quick PHP-ing to analyze a file of phished MySpace passwords that he had found. For those that don’t know what’s been going on with MySpace and the password phishing, check out this article for an explanation.
So armed with this data, I sat down and imported the file into a MySQL database, cleaning up bits and pieces, and then wrote some scripts to pull out useful data. Not content with just info on the emails and passwords, I started playing around with MySpace’s search page, and wrote a screen scraping script to grab the info of all the users by searching for their emails. It took a few hours to gather all the data, but then I was able to run some useful reports on it. I’ll let you check out Lolo’s full write-up on the thing, including the stats over on his article: Demographic Info From 26,000 Phished MySpace Accounts. If there’s any interest/demand, I’ll clean up the scripts and post the code.
What is my hard drive doing?!
Filed Under Geek, Video | 2006-10-09, 13:10
Ever wondering what goes on in that box as it makes little noises and the light flash? LeTheOnline.net took the top off one and turned on the computer to show you. And another video showing a demo of a harddrive with a little more educational content:
Secure your code!
Filed Under Geek | 2006-10-07, 14:06

Google has launch it’s new Google Code Search which allows you to search publicly accessible source code. Great for programmers, great for hackers, bad for not so attentive webmasters. Google crawls websites and peeks inside archive files (.tar.gz, .tar.bz2, .tar, and .zip) looking for code. Remember when you figured a zipped up file wouldn’t be spidered by a search engine? Not anymore. So check your websites, make sure you don’t have anything sensitive in those zip files in a clear-text text file. Want to know how easy it is to find useful information for not-so-nice actions? Check out this search for the config file for WordPress that contains your database information.
While I think Google has the best intentions, I don’t think this search is going to be a positive thing. The amount of code that might be accidentally exposed as well as the number of people just plain copying code is a bit much. If people want to put their code out there, they should just post it on a website to let all the search engines crawl it.
Where’d my Internet go?
Filed Under Geek | 2006-10-06, 23:30
The last week or so my internet connection has been going down seemingly randomly. It’ll go down for awhile and then come back just like normal. What made it odd was that a friend in Texas (I’m in Chicago) was also going down at the same times. After 3 or 4 “coincidences” we decided this wasn’t normal. After narrowing down the similarities, we started looking at our routers, both Linksys WRT54G running the hacked DD-WRT firmware. While it wasn’t a problem with a router, this focused my attention to where I would find the necessary clues.
The next time I lost my connection I noticed the led on my WRT54G router for “Internet” blinking like crazy, indicating a large amount of traffic. I couldn’t even access the router across my lan. I unplugged the router from the cable modem and instantly got access to the web interface. Plugged it back in, no access. Plugged directly into the cable modem with my desktop and got a solid connection again. Whatever is coming through doesn’t affect my Windows machine.
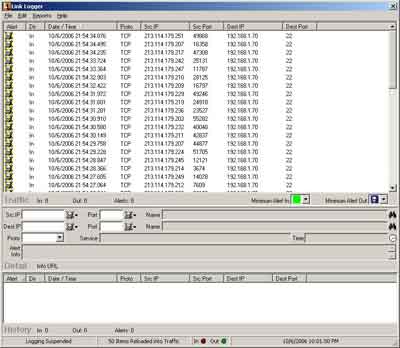
Logging is always good, so I downloaded Link Logger and setup DD-WRT to log to my desktop (see below for how-to) and waited. Sure enough I lost a connection about an hour later. Luckily all the evidence I needed was sitting in Link Logger.
Looks like someone from .se was trying to hammer on my ssh server with multiple machines. Since there are so many machines and so many attempts it was holding me down and not letting anything else through. A typical denial of service. So I unplugged the desktop from the router, plugged directly into the cable modem, power reset the modem to get a new dhcp lease, and started figuring out how to drop the ssh packets. I ssh’ed into DD-WRT while it was not plugged into the internet, and ran the following command line:
iptables -A INPUT --source 213.114.179.0/24 -j DROP
(This will block all incoming traffic from 213.114.179.*)
Of course when I plugged back in, he was no longer hammering, and I didn’t get a chance to test it. I dropped into the DD-WRT web interface, under Administration->Diagnostics and added the iptables command so it will run on startup. This way when I reboot the router it will still have that rule. Let’s hope that stops this mess.
While discussing this with my friend in Texas, we realized the true link between us and these Swedes was not our router, but rather our use of DynDNS. DynDNS is a quick (free) way to get an easy to remember domain that resolves to your home connection. We both have *.homeip.net addresses. I’d be willing to bet these wankers were just scanning for people with homeip.net addresses. Another clue to this was the fact that the attacks were still occurring with IP changes. DD-WRT has an option to automatically update your DynDNS name when your IP changes.
IP Addresses logged: (I wasn’t able to capture all of them as the Trial version of Link Logger doesn’t save them)
213.114.179.203
213.114.179.207
213.114.179.209
213.114.179.210
213.114.179.211
213.114.179.212
213.114.179.214
213.114.179.217
213.114.179.219
213.114.179.224
213.114.179.229
213.114.179.232
213.114.179.236
213.114.179.242
213.114.179.245
213.114.179.247
213.114.179.249
213.114.179.251
All of these resolve to *.cust.bredbandsbolaget.se.
How to log from your router
(This applies to DD-WRT v23 SP1 final)
- Log into the web interface for DD-WRT and go to Administration->Services
- Scroll down and enable “System Log”
- Save Settings
- Scroll back down and provide the IP address of the machine you want to log to.
- Save Settings
- Go to the Administration->Log tab
- Enable the Log, set the Log Level to High, and everything to On (this way everything gets logged)
- Save Settings
- Download and install Link Logger
- Point it to your router’s IP if necessary (Edit menu->Setup->Router Tab)